1. Introduction
The password is somewhere hidden in this app. Extract it. The password is the flag.
2. Analysis
First I’ll open the package with jad-x-gui
The following AESUtil part looks interessting:

Note: We can see the AES encryption key and the initialization vector
public class AESUtil { private static final String ENCRYPTION_IV = "SHCUOkfd89ut7777";
private static final String ENCRYPTION_KEY = "Simpleji4todnkfL";
From the encryption key a sha256 cryptographic hash value will be genereated (also called sha256.digest)
static Key makeKey()
{ try
{ return new SecretKeySpec(MessageDigest.getInstance("SHA-256").digest(ENCRYPTION_KEY.getBytes("UTF-8")), "AES");
The second part which looks interessting is located in LoginViewModel:

We have a closer look at the following byte orders:
public class LoginViewModel extends ViewModel {
private static byte[] exs = {-28, 73, 79, 78, 113, 73, 101, 98, 115, 6, 27, -35, 111, -55, -114, -11, -29, 0, -73, 91, 115, -24, -4, -94, -59, 43, -57, 112, 11, -54, -115, 2};
3. Decryption process
Calculating the SHA256 value of the encryption key:
https://xorbin.com/tools/sha256-hash-calculator

For the next step I’ll use Cyberchef
https://gchq.github.io/CyberChef
The Cyberchef Recipe looks like this:
Input:
-28, 73, 79, 78, 113, 73, 101, 98, 115, 6, 27, -35, 111, -55, -114, -11, -29, 0, -73, 91, 115, -24, -4, -94, -59, 43, -57, 112, 11, -54, -115, 2
From Decimal
Delimiter: Comma
Support signed values: yes
AES Decrypt
Key: d6eadb48382e79d35f25cbca4fb55ef69d842ee79ad843b4bae757fa99344d1a
Initialization Vector: SHCUOkfd89ut7777
Mode: CBC
Input: RAW
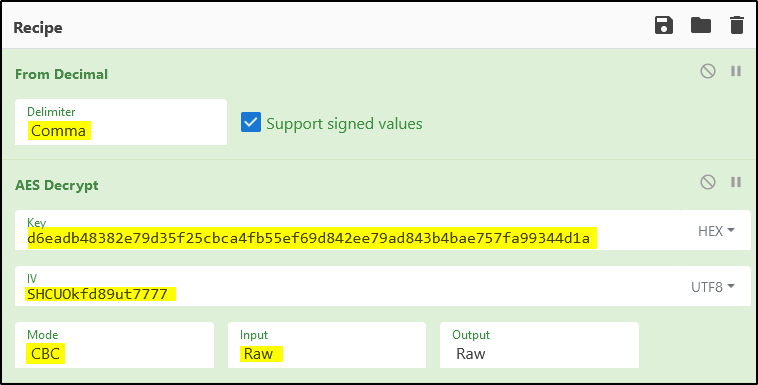
Output: HL{R3v3rsing.FUN}
Cyberchef Recipe:
From_Decimal('Comma',true)
AES_Decrypt({'option':'Hex','string':'d6eadb48382e79d35f25cbca4fb55ef69d842ee79ad843b4bae757fa99344d1a'},
{'option':'UTF8','string':'SHCUOkfd89ut7777'},'CBC','Raw','Raw',{'option':'Hex','string':''},{'option':'Hex','string':''})

