1. Introduction
Some web applications disclose the existence of valid usernames in some way to the user. This often happens with a login page which tells you whether the username exists on the system or not. This is called a user enumeration vulnerability of the bruteforceable type, as we can run a dictionary attack to get a list of valid users. Another type of user enumeration vulnerability is called dumpable in which the application provides a list of all users by itself.
In both cases, an attacker can use a list of valid usernames later to run a dictionary or bruteforce attack against the users‘ passwords.
Given is a list of valid usernames/passwords
Username: hacker10, hacker11, ..., hacker40
Password: compassYour goal is to exploit the vulnerability to compile a list of existing usernames.
2. Manual testing
Try to login with valid username and wrong password:

The message is: Wrong password.
Let’s try to login with a wrong username:
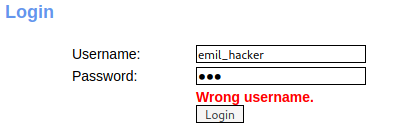
The message is: Wrong username.
Let’s try a common username like admin
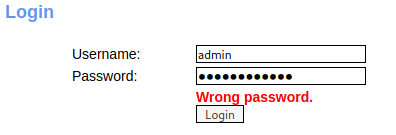
The message is: wrong password
Just by simple guessing I discovered a valid username 🙂
Let’s try to automate this!
3. Using Interception Proxy Burp
Go to History and start intruder for the POST request.

First I’ll clear all the variables except username

For the payload I’ll load a short list of usernames
https://github.com/danielmiessler/SecLists/blob/master/Usernames/top-usernames-shortlist.txt
For a larger attack and more enumeration, we can try a list of possible usernames that were collected from a honeypot project:
https://pw.fabian-fingerle.de/
Because this is a very time consuming task, I decided to use the short list and add a few known usernames to the list instead.
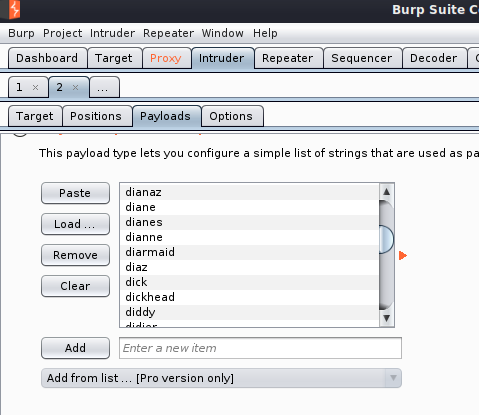
I want to test for the string wrong password.
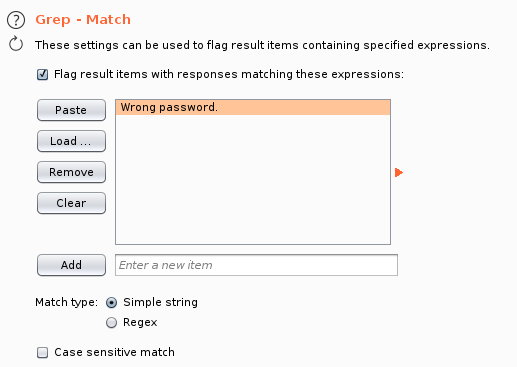
Let’s start the attack:
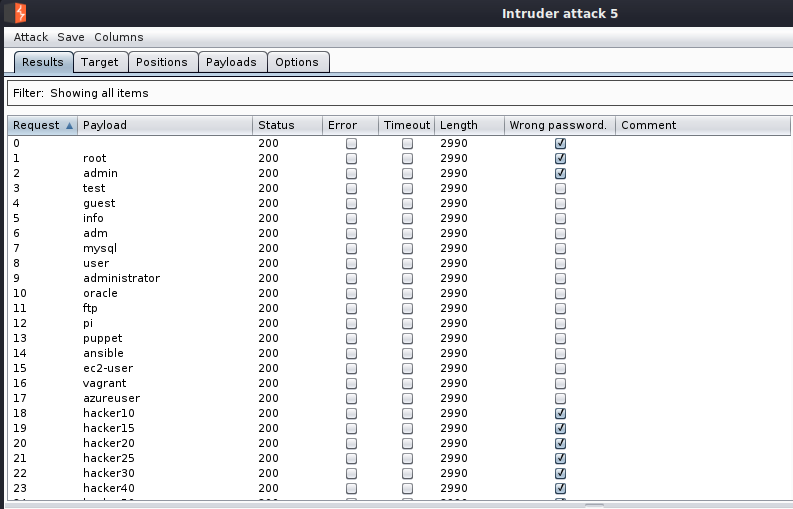
Beside the known usernames I did enumerate that the username root or admin could also be a valid target.
4. Summary and Mitigation
Because of the Login error message, an attacker can easily guess which usernames allredy exists and which not.
With that information and some time an attacker can try a bruteforce attack against a list of valid usernames.
Login form
- Make sure to return a generic “No such username or password” message when a login failure occurs.
- Make sure the HTTP response, and the time taken to respond are no different when a username does not exist, and an incorrect password is entered.
Password Reset
- Make sure your “forgotten password” page does not reveal usernames.
- If your password reset process involves sending an email, have the user enter their email address. Then send an email with a password reset link if the account exists.
PDF Report
enumeration

