1. Introduction and description
dnscan is a python wordlist-based DNS subdomain scanner.
The script will first try to perform a zone transfer using each of the target domain’s nameservers.
If this fails, it will lookup TXT and MX records for the domain, and then perform a recursive subdomain scan using the supplied wordlist.
Please answer the following questions:
- Is dnscan communicating directly with the authoritative DNS server or does the analysis take place via an open DNS server.
- What is the source IP address of the DNS packets arriving at the authoritative DNS?
- Can the DNS administrator of the authoritative DNS find out from which ip the DNS scan is performed?
2. Answer
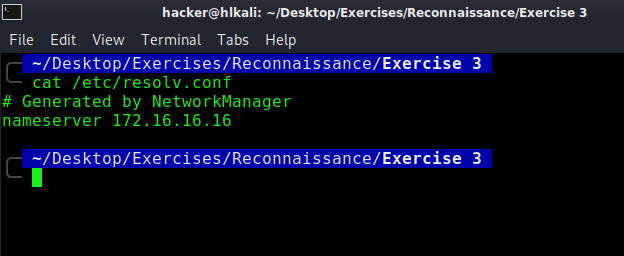
- Yes, dnscan will use the DNS Servers that are configured on my system and won’t use an open one.
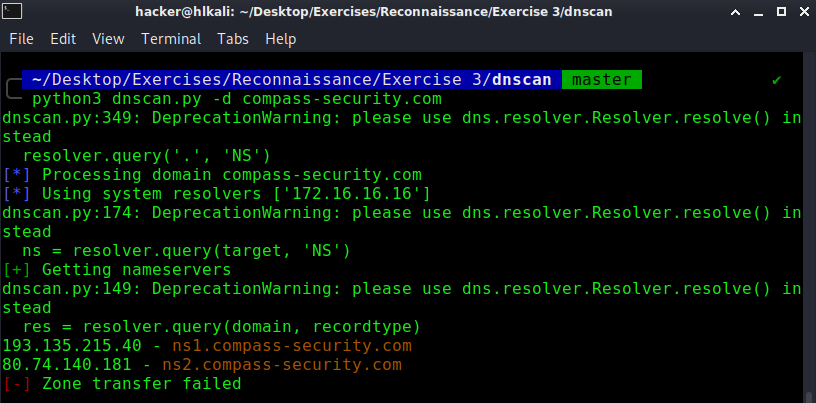
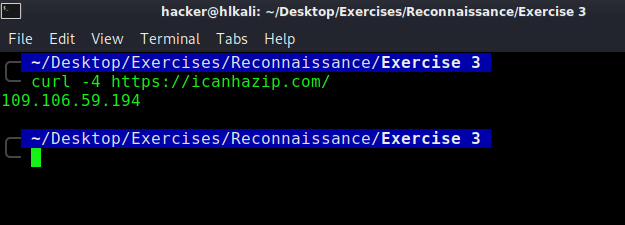
- Source IP Address will be my public IP Address
- I’d say yes, but if every query got logged, there will be tons of logfiles generated there. An attacker can easily hide his public ip adress by using a proxy or vpn connection.
Additional notes:
As the recursive bit is set in dns (see image below), your internet provider dns will do the job for you. This dns is like a "proxy* that will recursively resolve ip addressses. In the log of the authorative dns one will see your providers dns and not your own external ip of your internet connection.

PDF Report:
dnscan#1

