1. Introduction
This challenge is about JSON Web Tokens (JWT) and JSON based access tokens.
They are typically used to exchange the identity of a user between an identity provider and a service provider on a third party system.
Analyze how the JSON tokens are being used in the vulnerable web app and finally get discounts on the product.
You must analyze, understand and change the JWT token in this challenge.
2. Requirements
- Web Browser
- URL of vulnerable application (Cowbell Shop Docker Instance)
- ZAP Proxy
- Fiddle around with the /api/ url logged in and logged out and have a look in the headers to check for the Authorization: Bearer token
3. Information Gathering
Login with an exiting username and password to the Cowbellshop application.
username: customer0
password: compass0
Open the network tools in browser by hitting CTRL + Shift + I.
In the XHR tab you can filter for XHR requests. There you can find for example the calls GET latest and GET toprated. (see image below)
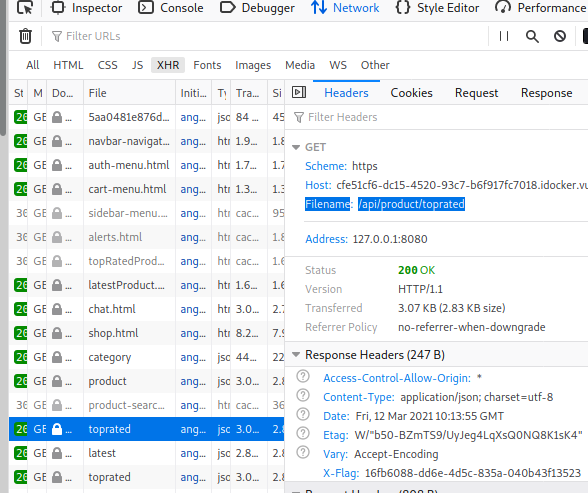
These two requests make a GET request to the URL https://{DOCKER_ADDRESS}/api/product/
We conclude, there is an /api/ endpoint that seems to be interesting from an API security perspective.
In the next step, we want to check if we can request the API by hand.
4. API Analysis
Now let’s see what we get when we open the /api/ path in browser.

There we can find an interessting hint:
GET /api/retailer/order/:orderId/applyDiscount/
orderId
As a retailer, you can apply a 50% discount to any order which is paid by bill.`
Maybe we can get a discount if the /api is not protected sufficiently?
In the next step we need to find a valid order, because the :orderId is being used in the API request.
To do this, use the browser tab where you have opened the webshop. Open the Orders page from the menu in the top right corner. Such a valid order ID can be 5acb4be9d9520729d8638c9a

5. Try to apply discount
I’ll try to apply a discount by entering the following URL:
https://{DOCKER_ADDRESS}/api/retailer/order/5acb4be9d9520729d8638c9a/applyDiscount/
This won’t work:

For the next step we need an interception proxy.
It is now our plan to intercept the HTTP request with the ZAP Proxy and manually adding the missing JWT token of the current user customer0 and bypass the authorization error.
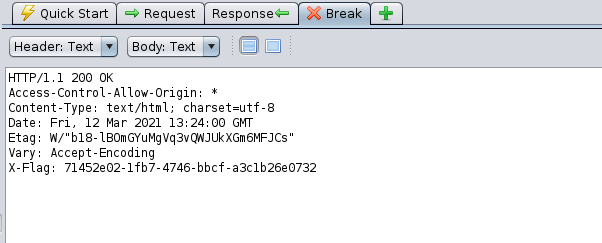
In your ZAP application search for /api and copy the Authorization: Baerer header (see picature below)


I’ll copy the authorization baerer header to inject it later. In the zap proxy history I search for the Apply discount URL and set a breakpoint there:

I reload the page again and inject the authorization baerer header.
Authorization: Bearer eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc1JldGFpbGVyIjpmYWxzZSwiX2lkIjoiNWFhMDQ4MWU4NzZkOWQzOWQ0Mzk3ODU5IiwidXNlcm5hbWUiOiJjdXN0b21lcjAiLCJmaXJzdG5hbWUiOiJKdWxpYW5lIiwibGFzdG5hbWUiOiJTY2h1bHplIiwiZW1haWwiOiJKdWxpYW5lLlNjaHVsemVAZ21haWwuY29tIiwiaWF0IjoxNjE1NTQzMzc4LCJhdWQiOiJzZWxmIiwiaXNzIjoid2Vic2hvcCJ9.E_o6dyUfvJAI2m4B-76Tpyql4gAEHUPAQdCzbLRYp7U
The attack didn’t succeed:

Where can we get a valid JWT Token?
Let’s try to inject the token from the API Documentation:


And let’s check the result:

If we check the order history we have a 50% discount:

Retrieve flag:
6. Summary and Mitigation
To inject the JWT token of customer0 didn’t work for some reason, but it was possible to use the JWT token from the API documention to get the discount.
To understand how JWT really works it needs a deeper understanding how the technology works than just solving this exercise.
The problem in that case may be that the JWT Lifespan wasn’t limited.
I did collect the following mitigation tipps:
JSON Web Tokens are very popular and are highly regarded for their convenience. If used correctly, JWT can prevent errors of inadequate authorisation, allow simple and easy distribution of information flows between the servers, organise a single entry-point for various services with the same login data and even increase the service efficiency.
However, if misused, this technology may put entire systems at risk, which may even result in an all-out compromise of the login credentials for all system users.
To conclude, in order to make the JWT use safe and secure, it is recommended to:
- Use secure connection when transferring tokens;
- Never transfer users’ sensitive data in the tokens;
- Limit JWT lifespan and use “refresh tokens” mechanism;
- Use long key phrases;
- Keep a white list of authorised signature algorithms on the application side;
- Work, ideally, with one signature algorithm only;
- Choose well-known and reliable libraries for JWT operation;
- Always validate and sanitise the data received from users.
7. Further Readings
https://cyberpolygon.com/materials/security-of-json-web-tokens-jwt/
https://curity.io/resources/architect/api-security/jwt-best-practices/
https://www.sjoerdlangkemper.nl/2016/09/28/attacking-jwt-authentication/
PDF Report
jwt#1

