Lab: Maintaining Access
Step 5 – Credential Dumping on Windows 10 Client
Teamwork – Team DaMa
1. Introduction
If you have local administrative privileges on a Windows machine, you can abuse this to retrieve various forms of credentials stored on the respective machine. This includes credentials of local user accounts (stored in the SAM file) as well as temporarily cached credentials of currently logged-in users (kept in the memory of the lsass process).
There are many ways to do this. In this exercise we will use the famous tool Mimikatz.
Please write a short PDF report that includes screenshots of the major steps of the attack (at least the final step) and answer the following questions:
- Why does Mimikatz need debug privileges?
- What are the prerequisites that your current session has SeDebugPrivileges
- What are you going to do next with the NTLM hash of user Aalfort?
- Explain what Mimikatz does in the background to reveal these credentials?
- Why can user Aalfort’s credentials be found in the LSASS memory of Client1
2. Answers
-
Mimikatz requires this privilege as it interacts with processes such as
LSASS.exe. Otherwise we won’t be able to dump sensitive informations from the memory.
In a Windows System the
LSASS.exeprocess is responsible for the following things:- Verifying and storing users credentials
- Writing to the windows security log
- Enforcing the security policy on the system
-
The
debug privilegeaccording to Microsoft determines which users can attach a debugger to any process or to the kernel. By default this privilege is given to Local Administrators!
We have two ways to go:- become
(local) Administrator - become
local system
- become
-
After gaining hashes it is up to the attacker to what they decide to do with the hash. They can try their hand at
crackingit. But as we all know that it is difficult, time-consuming, and still no guarantee of gaining the correct password. Then there is this other way. During authentication, the basic procedure is the password is collected from the user, then it is encrypted and then the encrypted hash of the correct password is used for future authentication. During Credential Dumping, we see that we have extracted lots and lots of hashes. Now as an attacker we don’t know the password. So, during the authentication, we provide the hash instead of the password. Windows compares the hashes and welcomes the attacker with open arm.https://crackstation.netis an online hash cracker service.Crackstation’s lookup tables were created by extracting every word from the Wikipedia databases and adding with every password list we could find. We also applied intelligent word mangling (brute force hybrid) to our wordlists to make them much more effective. For MD5 and SHA1 hashes, we have a 190GB, 15-billion-entry lookup table, and for other hashes, we have a 19GB 1.5-billion-entry lookup table.

Next step is allready part of the lateral movement. We’ve tried if we can access the
fs1server by trying thepass the hash attack.In Mimikatz we’ve used the following command:
sekurlsa::pth /user:aalfort /domain:winattack.local /ntlm:9859340265d3b3c1eb628ece70ebc238 /run:cmd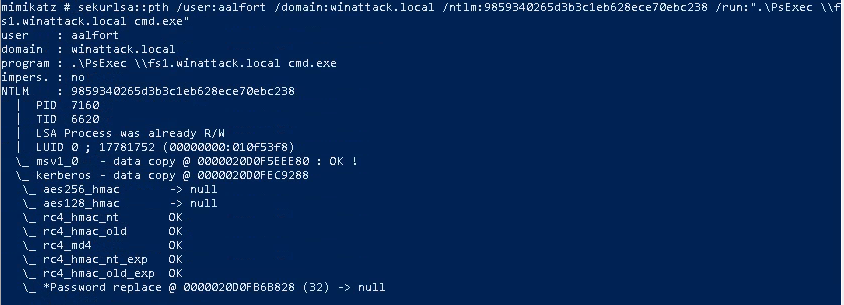
By using thepsexecutility we weren’t able to access thefs1fileserver, but this is not the goal of this exercise! -
Mimikatz is doing a memory dump of the process
LSASS.exeto generate an output of sensitive logon informations.
(See Screenshot of Step1) -
After the initial authentication, Windows keeps the hash in its memory so that the user doesn’t have to enter the password again and again. The User
Aalforthas an interactive session to our client and that’s the reason why we found theNTLM Hashin the memory.
PDF Report
Step5

