1. Introduction
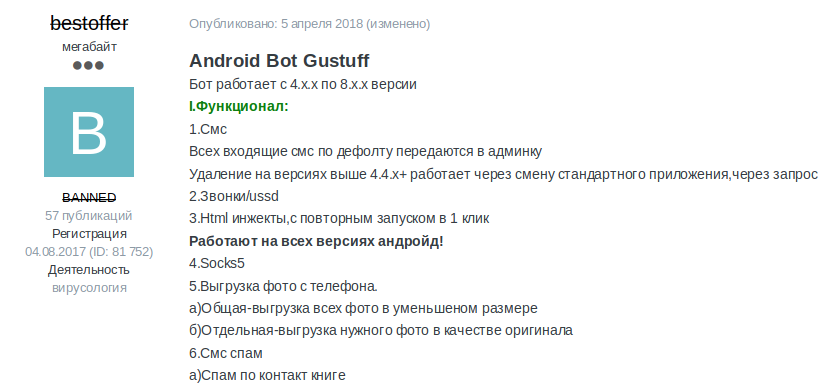
Researchers uncovered a malware known as „Gustuff“. The Gustuff malware is being advertised in the Exploit.in forum as a botnet for rent.
This is a sample of April 2021: c3U0e8kc52.apk.
Do not install the sample on a real device!
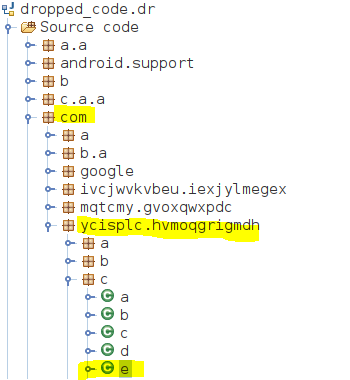
As the malware is packed and heavily obfuscated, the unpacked dropped code is provided.
In this training various features of „Gustuff“ shall be explored, such as:
- Emulator detection
- Setting / resetting the password
- Extract the list of attacked apps
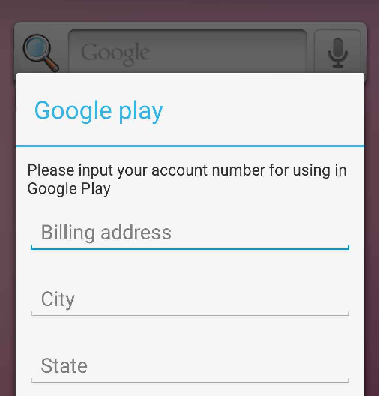
- The malware is phishing for Credit Cards (see screenshot below). Find the code.
- Extract the CC Server
2. Analysis
I’ll load the dropped code in jadx-gui and try to search for patterns first.

2.1 Emulator detection
Typical search patterns for emulator detection looks like this:
private fun checkBuildConfig(): Boolean {
var isEmulator = (Build.MANUFACTURER.contains("Genymotion")
|| Build.MODEL.contains("google_sdk")
|| Build.MODEL.toLowerCase().contains("droid4x")
|| Build.MODEL.contains("Emulator")
|| Build.MODEL.contains("Android SDK built for x86")
|| Build.HARDWARE == "goldfish"
|| Build.HARDWARE == "vbox86"
|| Build.HARDWARE.toLowerCase().contains("nox")
|| Build.FINGERPRINT.startsWith("generic")
|| Build.PRODUCT == "sdk"
|| Build.PRODUCT == "google_sdk"
|| Build.PRODUCT == "sdk_x86"
|| Build.PRODUCT == "vbox86p"
|| Build.PRODUCT.toLowerCase().contains("nox")
|| Build.BOARD.toLowerCase().contains("nox")
|| (Build.BRAND.startsWith("generic") && Build.DEVICE.startsWith("generic"))) return isEmulator
}
A quick search for strings like qemu, genymotion… shows where the emulator detection takes place:
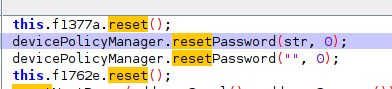
2.2 Setting / resetting the password
I search for strings like reset, password and reset password. I guess this result could be a match:

}
@TargetApi(8)
public static void a(Context context, String str) {
DevicePolicyManager devicePolicyManager = (DevicePolicyManager) context.getSystemService("device_policy");
if (devicePolicyManager.isAdminActive(new ComponentName(context, gcbkxQXT.class))) {
Log.i("TAG", "Set password.");
devicePolicyManager.resetPassword(str, 0);
return;
}
Log.i("TAG", "Not an admin");
}
2.3 list of attacked apps
Let’s check the screenshot from the forum where the malware was advertised:

Let’s search for example westpac.bank and see what we get:

To extract the list of possible attacked apps I use cyberchef:
bcc.org.freewallet.app com.hashengineering.bitcoincash.wallet com.btcontract.wallet piuk.blockchain.android org.stgeorge.bank de.schildbach.wallet lt.spectrofinance.spectrocoin.android.wallet co.edgesecure.app com.citibank.mobile.au org.electrum.electrum me.cryptopay.android net.bither au.com.nab.mobile com.coincorner.app.crypt com.arcbit.arcbit com.xapo com.qcan.mobile.bitcoin.wallet secret.pattern com.plutus.wallet org.westpac.bank btg.org.freewallet.app org.banksa.bank org.bom.bank com.kibou.bitcoin distributedlab.wallet com.airbitz com.anz.android au.com.bankwest.mobile com.bitcoin.mwallet com.bitcoin.wallet com.coinspace.app com.wirex com.bitpay.wallet com.commbank.netbank com.aegiswallet au.com.ingdirect.android secret.access com.coinbase.android btc.org.freewallet.app com.circle.android de.schildbach com.anz.android.gomoney eth.org.freewallet.app com.kryptokit.jaxx bcn.org.freewallet.app com.bitpay.copay
2.4 Credit card phising
This is a possible screen overlay of google playstore to trick the victim to enter sensitive informations like credit card numbers.
Such attacks are known as TapJacking
I search for possible strings like layout_inflater and windowsManager.addView
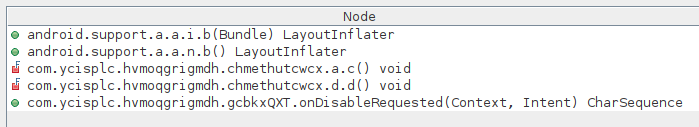

Possible Screen changes?
}
public void c() {
}
public boolean d() {
return true;
}
public int e() {
return this.f298c;
}
/* access modifiers changed from: package-private */
public Activity f() {
return this.f296a;
}
/* access modifiers changed from: package-private */
public Context g() {
return this.f297b;
}
/* access modifiers changed from: package-private */
public Handler h() {
return this.f300e;
}
/* access modifiers changed from: package-private */
public p i() {
return this.f299d;
}
/* access modifiers changed from: package-private */
public boolean j() {
return this.g;
}
2.5 Search for the CC Server
I’ll try the following Regex String to search for IP Addreses:
\d+.\d+.\d+

Result:

Possible CC Server?
88.99.169.198
If I follow the variable f1341c I get this:

(There is a possible connection to a server, but I got stuck here..)
Another idea is to search for the ending .php, because the backend connects often to a php URL.

After trying to follow the code here I got also stuck and I’ll stop here. I was not able to find the CC Server inside the Code
From virustotal I could see several reports linked to JoeSandbox.
https://www.joesandbox.com/analysis/416538/0/html
From one of this reports I get a list of IP Addresses:

The first IP address above is not on the list, but I marked the german one.

