1. Introduction
An Android malware sample called "RedAlert" was found in the wild. The malware is known to collect data from infected phones and turns them to a remote controlled bots. You have to find out the address of the Command & Control (CC) server of the bots.
- Download the APK sample.
- Extract the APK (apktool or jadx-gui)
- Analyze the resources
Your goal is
- to Extract the Android Package,
- Check the Android Permission (Check if it can intercept and write SMS messages)
- Find the CC server address (Protocol,IP, Port) in the resource files
2. Analysis
The permissions are stored in the manifest.xml file of the apk package.
I’ll use the aapt tool to dump the permissions.
aapt dump permissions red_alert.apk
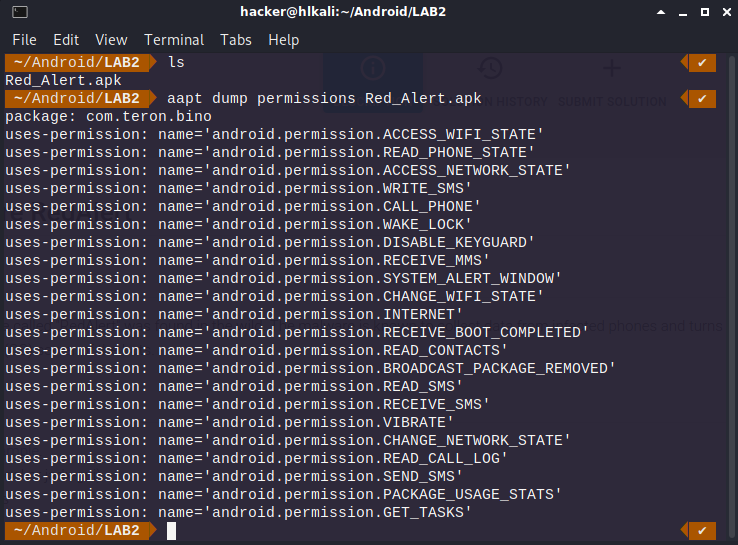
The package has the permissions to write and send sms.
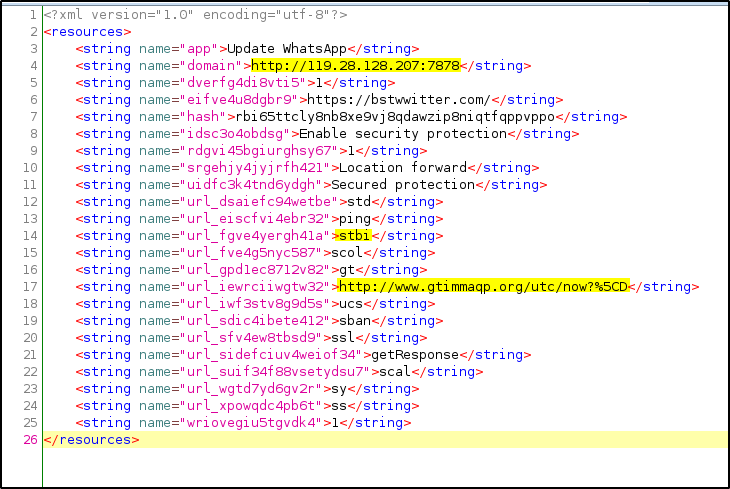
Let’s open the apk file with jadx-gui and have a closer look at strings.xml

Here we get a list of potential malicious domains:
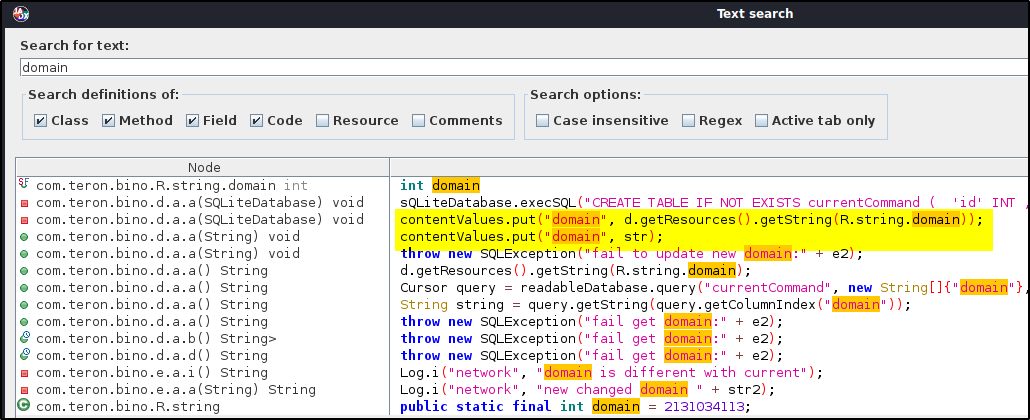
Another approach we can do is to search for domain inside jadx-gui
Maybe the CC Server URL will add a string from the list above. I’ll upload the apk file to virus total and get this graph:
Note: We can see the string /stbi
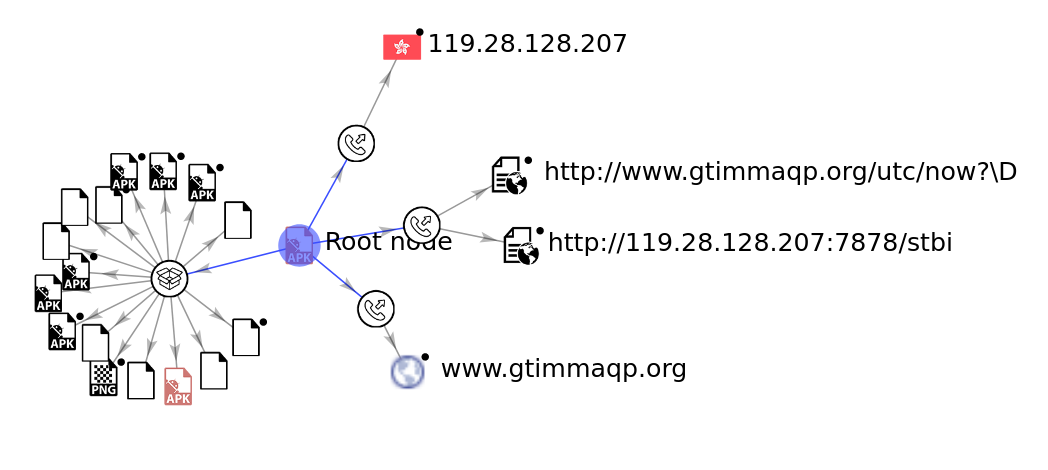
Potential CC Server:
IP: 119.28.128.207 (CN)
Protocol: http
Port: 7878

