1. Introduction
Now we want to test our defenses. This is called Purple Teaming. Learn more about it in this challenge.
Red and blue teaming are well established concepts in information security, but recent years have given rise to a new, collaborative approach – purple teaming.
2. Tooling
Atomic Red Team is a set of scripts or atoms to test your detection based on MITRE’s ATT&CK.
Open a PowerShell on your Live CD:
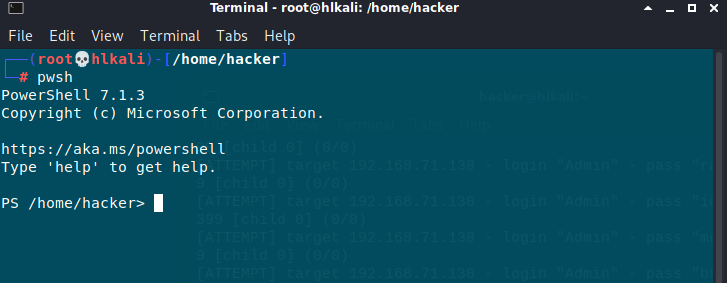
Install Atomic Red Team Scripts
IEX (IWR ‚https://raw.githubusercontent.com/redcanaryco/invoke-atomicredteam/master/install-atomicredteam.ps1‚ -UseBasicParsing);
Install-AtomicRedTeam -getAtomics -Force
Connecting to Win10 VM using WinRM:
$sess = New-PSSession -HostName 192.168.71.150 -Username Cybercop
Connection is succesful!

After this is done, we can start testing the detections for persistence. Please test the following cases:
- T1546.008 Accessibility Features
- T1098 Account Manipulation
- T1546.010 AppInit DLLs
- T1546.011 Application Shimming
- T1053.002 At (Windows)
- T1197 BITS Jobs
You can find descriptions for these in the section Persistence on:
3. Testing
Can you identify any detection gaps?
Note: the rules are triggered every 5 minutes
Example execution:
Invoke-AtomicTest T1546.008 -Session $sess -GetPrereqs
Invoke-AtomicTest T1546.008 -Session $sess
Cleanup
Invoke-AtomicTest T1546.008 -Session $sess -Cleanup
T1546.008 – Accessibility Features
Image File Execution Options Injection got detected. Replace binary of sticky keys not.

T1098 – Account Manipulation / Domain Account and Group manipulate
Kibana Dashboard shows no Detection. My target W10 target Machine is a German setup. There is no Group name called "Administrators". The second test could be failed because this machine is not AD joined and there is no Actice Directory Webservice running.
T1546.010 – AppInit DLLs
Kibana Dashboard shows no Detection. Only powershell download of T1546.010.dll got detected


T1546.011 – Application Shimming
Kibana detects download of AtomicTest.dll and potential Application Shiming.



Registry keys related for T1546.011 got not detected!

T1053.002 At (Windows)

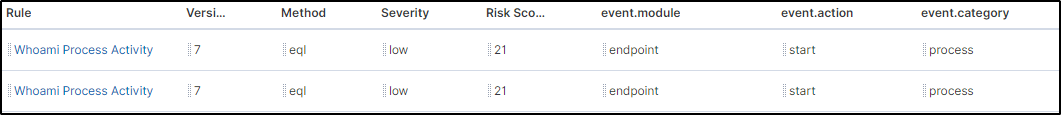
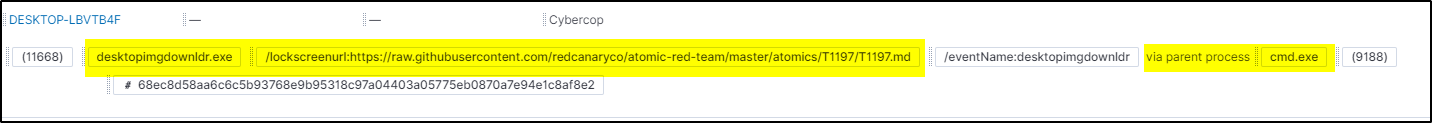
T1197 BITS Jobs
Only bitsdownload via cmd.exe got detected

4. Summary
| ATT&CK ID | Test performed | Test Detected | Comments |
|---|---|---|---|
| T1546.008 | Attaches Command Prompt as a Debugger to a List of Target Processes windows | Yes | |
| T1546.008 | Replace binary of sticky keys windows | No | |
| T1098 | Admin Account Manipulate windows | No | |
| T1098 | Domain Account and Group Manipulate windows | No | PreReq Failed. Test Machine is not AD joined |
| T1546.010 | Install AppInit Shim windows | No | |
| T1546.011 | Application Shim Installation windows | Yes | |
| T1546.011 | New shim database files created in the default shim database directory windows | Yes | |
| T1546.011 | Registry key creation and/or modification events for SDB windows | No | |
| T1053.002 | At.exe Scheduled task windows | No | Not supported on Win10 |
| T1197 | Bitsadmin Download (cmd) windows | No | |
| T1197 | Bitsadmin Download (PowerShell) windows | No | |
| T1197 | Persist, Download, & Execute windows | No | |
| T1197 | Bits download using desktopimgdownldr.exe (cmd) windows | Yes |

