Assignment Series #A3 Intro and Historical Crypto
1. Introduction
This challenge will provide an intro into the foundation of information security, cryptography and a few historical developments. Follow the questions to direct your self-study. Check the theory module or consult Wikipedia if you happen to struggle answering a question.
-
While most use CIA as the foundation for Information Security some add further words to complete it. Name two more commonly used to enhance the triad?
-
Cryptography is usually used to achieve or provide a so-called cryptographic service. Name methods or functions (aka cryptographic primitives to achiev the listed services)
- Data secrecy
- Data integrity
- User verification
- Non-repudiation
-
We usually refer to Alice and Bob as parties that exchange information. Could you name three more personas that have a special meaning in crypto? Eg. Mallory for someone that does malicious things.
-
Draw a basic crypto system and name all inputs, outputs, intermediate products, processes as well as all involved parties above.
-
Assuming Malory has no access to Alice and Bobs facilities but is in position to interfere with and to snoop on the messages they exchange. Can you point out the difference between active and passive attacks which Mallory could apply? Give examples for both.
-
Alice and Bob could make use of two major concepts to secure their messages. Either use a symmetric cipher systems or a public key cipher systems. Explain the difference based on Wikipedia, Cryptography, Modern Cryptography, Sections Symmetric and Public-key encryption.
-
Genious engineers such as Alice are capable to developed their own algorithms to secure messages. Is it a wise decision to keep the algorithms secret? Discuss pros and cons.
-
What you didn’t know is that Alice and Bob lived in 1580 and both were fluent in English. They left us a treasure. Unfortunately, all we know about it is a cryptic message "Jcctz Ntwgbz Qcl. Kptd kq pwfc hgiae dwatmddhsctj ogaigaegb dmddcev iyo K yd dpca ecio jqs jwwggb zb. Hpnj uwyp!". Do you know what it means? Hint: its a classical cipher and could be broken either by using Crypttool or an online tool.
-
Can you provide details on the algorithm and key in use?
-
Is a cipher text properly protected if we make sure to have large keys? May you provide an example with the simple substitution cipher?
-
If Alice and Bob had choosen to hide the message with a One-Time Pad. Could we decipher it? Name three things they needed to keep attention on to have perfect secrecy and thus to avoid an attacker could recover the plain-text?
2. Answers
-
In this case CIA doesn’t stand for a secret agency. It’s a common term to summarize the purpose of crypto in three words
Confidentiality,IntegrityandAuthenticity. Two further words to enhance the triad areAccountabilityandNon-repudiation. -
Some examples of cryptographic primitives are:
- Symmetric key cryptography
- Public-key cryptography
- One-way hash function
- Digital Signatures
- Pseudo random number generator (PRNG)
- Authentication
- Mix network
-
Some more common names used are:
name function Chuck A third participant, usually of malicious intent Craig A password cracker, often encountered in situations with stored passwords Eve An eavesdropper, who is usually a passive attacker.
-
Picture shows basic crypto system with assymetric key (public key encryption):

-
Passive Attacks are in the nature of eavesdropping on or monitoring of transmission. The goal of the attacker is to obtain information is being transmitted. Active attacks involve some modification of the data stream or creation of false statement.
Passive Attack example(Traffic analysis):
Suppose that we had a way of masking (encryption) of information, so that the attacker even if captured the message could not extract any information from the message.
Mallory could determine the location and identity of communicating host and could observe the frequency and length of messages being exchanged. This information might be useful in guessing the nature of the communication that was taking place.

Active Attack example(Modification of messages):
It means that some portion of a message is altered or that message is delayed or reordered to produce an unauthorised effect. For example, a message meaning “Allow JOHN to read confidential file X” is modified as “Allow Mallory to read confidential file X”.

-
Symmetric-keycryptography use a single key for encryption and decryption:

Public-keycryptography, use different keys for encryption and decryption:

-
Kerckhoffs‘ principle states that the security of a system must not depend on the secrecy of the algorithms, but only on the secrecy of a key. Keeping informations about the algorithm secure doesn’t mean that you’ll gain more security.
We can compare the same principe withopensourceandclosed-sourcesoftware. Like many other areas of software engineering, the development of encryption mechanisms is based on the assumption that open source does not compromise security. Rather, a consistent application of Kerckhoff’s principle leads to the fact that errors in cryptographic algorithms are detected more quickly, since corresponding procedures must withstand the critical eyes of the experts. -
Encoded message:
Jcctz Ntwgbz Qcl. Kptd kq pwfc hgiae dwatmddhsctj ogaigaegb dmddcev iyo K yd dpca ecio jqs jwwggb zb. Hpnj uwyp!
I use a online tool for analysis of the chiffre: https://www.boxentriq.com/code-breaking/cipher-identifier
Vigenere Ciphergot the highest result, so let’s try that!https://www.boxentriq.com/code-breaking/vigenere-cipher
With the key
CyrillI can successfully decode the message:hello crypto fan this is your first successfully decrypted message and i am very glad you solved it well done
-
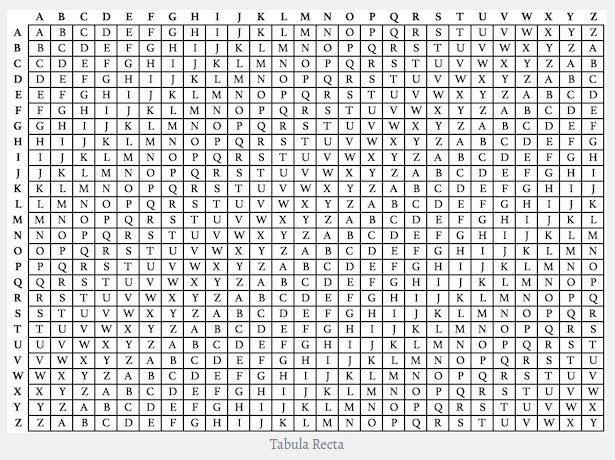
In the Vigenère cipher, a message is encrypted using a secret key, as well as an encryption table (called a Vigenere square, Vigenere table, or tabula recta). The tabula recta typically contains the 26 letters of the Latin alphabet from A to Z along the top of each column, and repeated along the left side at the beginning of each row. Each row of the square has the 26 letters of the Latin alphabet, shifted one position to the right in a cyclic way as the rows progress downwards. Once B moves to the front, A moves down to the end. This continues for the entire square.
-
Security can be increased by using large keys, but it depends on the cipher. By using the simple subsitution cipher max. key lenght is 26. Although the number of possible substitution alphabets is very large, this cipher is not very strong, and is easily broken.
Using this system, the keyword "zebras" gives us the following alphabets:
Plaintext alphabet: ABCDEFGHIJKLMNOPQRSTUVWXYZ
Ciphertext alphabet: ZEBRASCDFGHIJKLMNOPQTUVWXY
A message
flee at once. we are discovered!
enciphers to
SIAA ZQ LKBA. VA ZOA RFPBLUAOAR!
- OTP encryption isn’t breakable, but it must:
- be at least as long as the message,
- equally distributed randomly,
- remain secret and
- may not be reused, even partially.
PDF Report:
Hystorical_Crypto#1

